15 Things People Pretend to Know About Technology
Tech shapes how you live, work, and connect, but it’s easy to feel lost in the details. Many people act like they know more than they do when it comes to technology.
This article uncovers common tech topics people bluff about and explains how they really work.
How Blockchain Actually Works

Think of blockchain as a special kind of digital record book. Instead of one person or company keeping the book, many people share copies of it.
This makes it harder to cheat or change the information. When you make a transaction, like sending money, your info gets encrypted.
That means it’s turned into a secret code. Many computers in the network check to make sure your transaction is real.
Once the transaction is confirmed, it joins a group of other transactions called a block. Each block links to the one before it, creating a chain.
No single computer controls the whole chain. Every computer, or node, works on its own but compares results with the others.
This keeps the information accurate and secure without needing a middleman.
What Quantum Computing Means

Quantum computing is a new kind of technology that works very differently from regular computers. It uses the strange rules of quantum physics to solve some problems much faster.
Regular computers follow strict, step-by-step rules. Quantum computers can look at many possibilities at the same time.
One big impact of quantum computing is on encryption. Quantum computers could eventually break the codes that protect your data.
Right now, quantum computers are still being built and tested. They have many errors and are not ready for everyday use.
But many companies are working hard to make them better.
The Basics of Cloud Computing

Cloud computing lets you use software and store data over the internet. Instead of keeping files on your computer’s hard drive, you access them through remote servers.
This means you can get to your information from anywhere with an internet connection. You don’t have to manage the hardware or install programs yourself.
The cloud handles the technical parts, so you only focus on using the tools you need. It also allows easy scaling, meaning you can use more or less storage and computing power as needed.
Many people think the cloud is slow or unsafe, but it can be both fast and secure. Cloud providers use strong security measures to keep your data safe.
Sharing resources in large data centers often saves energy and can be better for the environment.
How AI Algorithms Learn

You can think of AI algorithms as students trying to learn from examples. They start by looking at lots of data, like pictures, words, or numbers.
Each time they see new data, they try to find patterns that help them make decisions. The algorithm makes a guess, checks if it is right, and then adjusts itself.
This process repeats until the guesses get better. The way AI learns is not like how humans learn.
It uses math to adjust numbers inside its model. These small changes help the AI improve at tasks like recognizing faces or understanding language.
AI does not think or understand like a person. It only works by using rules and data to make predictions.
The Concept of 5G Technology

5G is the fifth generation of mobile network technology, coming after 4G. It uses radio waves, just like the networks before it, but with some upgrades.
5G means faster internet on your phone or computer. It can load videos and websites quicker, and it can support more devices at once.
This is helpful in crowded places like stadiums or busy city centers. 5G is more than just speed.
It changes how networks work by being more reliable and allowing new technologies like smart cars or remote medical care. Knowing the basic idea helps you see what it really does without getting caught up in myths or too much hype.
Understanding Cybersecurity Threats

Cyber threats come in many forms, like viruses, phishing scams, and ransomware. Each type can cause different problems for you or your devices.
Hackers often look for easy access, no matter the size of the target. You should always stay cautious, even if you think you’re not a big target.
Sometimes, people assume antivirus software will catch everything. While it helps, it’s not foolproof.
You also need good habits, like strong passwords and avoiding suspicious links. Cybersecurity threats change all the time.
Keep updating your software and learn about new risks to keep your data safe.
How Internet of Things (IoT) Devices Connect

When you use IoT devices, like smart lights or fitness trackers, they connect to each other and to the internet to share data. This happens through networks, often using Wi-Fi, Bluetooth, or other wireless signals.
Your devices talk without needing you to control every step. Each IoT device has sensors and software that help it collect information.
For example, a smart thermostat senses the temperature and sends data to your phone. This way, you can check or change settings from anywhere.
Your IoT devices also have unique IDs. This helps them recognize each other and keep the data moving correctly.
Many IoT devices can work together to make life easier. Your smart home system, for example, might connect lights, locks, and cameras into one network you manage with a single app.
What Big Data Really Is

Big data is a term used to describe huge amounts of information that are too large or complex for regular software to handle. You might hear about it in businesses, science, or even social media.
It’s not just about size. Big data includes many different types of information, like numbers, text, and images.
This variety helps businesses find patterns and make smarter decisions. Big data uses special methods, like machine learning, to analyze information and predict trends.
This can help you understand customer habits or improve products. Big data is different from regular data because it requires more powerful technology to manage and analyze it.
The Difference Between RAM and Storage
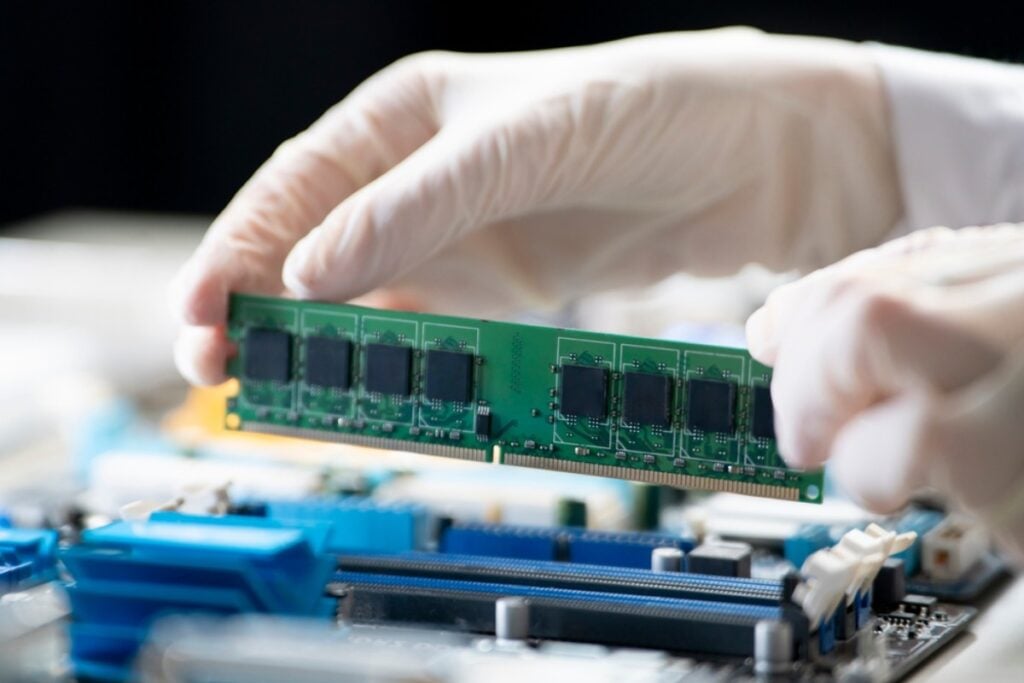
When you hear about a computer or phone’s memory, it can be confusing. People often mix up RAM and storage, but they do very different jobs.
RAM, or random access memory, is where your device holds data it is using right now. It helps your apps run fast and smoothly.
But RAM only works while your device is on. When you turn it off, RAM forgets everything.
Storage is like a big closet for your files, apps, and photos. It keeps everything saved even when your device is off.
The more storage you have, the more stuff you can keep. Think of RAM as your desk where you work on things right now.
Storage is your filing cabinet where you keep everything for later.
How Cryptocurrency Transactions Occur

When you send cryptocurrency, you are moving digital coins from your wallet to someone else’s wallet. Each wallet has a unique address that identifies it on the blockchain.
You need to use a private key, which is a secret code, to approve the transaction. This key proves the transaction is really from you.
After you send it, the transaction is shared with many computers called nodes. These nodes check if everything is correct, like making sure you have enough coins to send.
Once verified, the transaction is added to the blockchain. This ledger is a special digital record that everyone can see but no one can change.
Because transactions are on the blockchain, they are permanent. You cannot reverse or erase them after they are confirmed.
This whole process happens fast and without banks or middlemen.
Voice Recognition Technology

Voice recognition technology has been around since the 1950s. It works by turning your spoken words into digital data so devices can understand what you say.
You probably use voice assistants like Siri, Alexa, or Google Assistant. These tools make it easier to get information or control smart devices without touching a screen or keyboard.
Voice recognition isn’t just for convenience. It also helps people with disabilities and supports language learning.
Accuracy can vary depending on how clearly you speak or background noise. Privacy is another concern, as some devices record your voice data to improve services.
This technology is growing fast. Developers are working on making it smarter and safer for everyday use.
What Edge Computing Does

Edge computing lets your devices process data close to where it is created. Instead of sending everything to a distant data center, some work happens right on your device or nearby.
This helps things happen faster. Because the data is handled nearby, you get quick responses.
This is why smart devices and apps can work smoothly without delays. You might not notice it, but edge computing helps with real-time updates.
For example, your phone can quickly recognize speech or video without waiting for the internet to send data somewhere far away. It also helps save internet bandwidth.
Since less data travels far, this can make your connections more reliable. Smart home devices, self-driving cars, and even some games use edge computing to work better.
How Virtual Reality Functions

Virtual reality, or VR, works by creating a computer-made world you can see and sometimes hear or touch. When you wear a VR headset, it shows you images that change as you move your head.
This tricks your brain into thinking you are inside a new place. The system uses sensors to track your movements.
These sensors tell the computer where you are looking and moving. So, the images update quickly to match what you do, making the experience feel real.
VR also uses sounds and sometimes touch feedback, like vibrations, to make the world more believable. You might use controllers or gloves to interact with objects in VR.
Behind the scenes, VR combines hardware like displays and sensors with software that creates the virtual world. This technology tries to follow real-world rules, like how far away things look or how objects move.
The Role of Machine Learning

Machine learning is a part of technology that helps computers learn from data. Instead of being told exactly what to do, machines improve by finding patterns on their own.
This makes many things in your daily life smarter and more useful. You might have seen machine learning in action without realizing it.
For example, it powers recommendations on your favorite streaming or shopping sites. It also helps apps understand your voice or recognize faces in photos.
Even though machine learning sounds complex, its main idea is simple: teaching machines to get better over time. This doesn’t replace human thinking but helps you do more by expanding what technology can do.
How Encryption Protects Data

Encryption transforms your information into a secret code. When data is sent or stored, it becomes a mix of letters and numbers.
Only someone with the right key can turn it back into the original message. If a hacker tries to steal your data, they won’t understand it.
Encryption stops them from reading your emails, passwords, or credit card details. It also protects your data when you use the internet or cloud services.
Many tools, like BitLocker or FileVault, use encryption to guard data on your devices. This helps keep your files safe even if your device is lost or stolen.
Encryption matters for privacy too. It protects sensitive information, like your messages and personal photos, from being shared without your permission.







